
The Federal Bureau of Investigation (FBI) and the U.S. Cybersecurity and Infrastructure Security Agency (CISA) just warned of a Russian Intelligence Services (RIS) phishing campaign targeting “high intelligence value” individuals. The campaign targeted commercial messaging apps, with Signal accounts specifically identified as a primary target.
Signal has reportedly been used by both the U.S. Department of Defense, including Secretary Hegseth, as well as the Department of Government Efficiency (DOGE). Importantly, the FBI says the attackers did not break Signal’s encryption or hack the app itself, but instead used phishing to gain access to individual accounts.
According to the joint FBI/CISA report, the attacks successfully compromised “thousands” of individual Signal accounts linked to former U.S. government officials, military personnel, political figures, and journalists. This is especially concerning as a recent Department of Defense Inspector General’s report found that, in at least one instance, Hegseth’s communication of nonpublic information over Signal during last year’s bombing of Houthi forces in Yemen “created a risk to operational security that could have resulted in failed U.S. mission objectives and potential harm to U.S. pilots.”
How the phishing attack was carried out
The attack was implemented using standard phishing techniques. In this case, the FBI says the RIS sent messages masquerading as automated Signal support accounts. The messages were tailored to encourage their targets into taking an action, such as clicking a link or providing two-factor authentication codes and account PINs. In doing so, they provided the hackers direct access to their Signal account.
Samples of messages used were provided by the FBI.
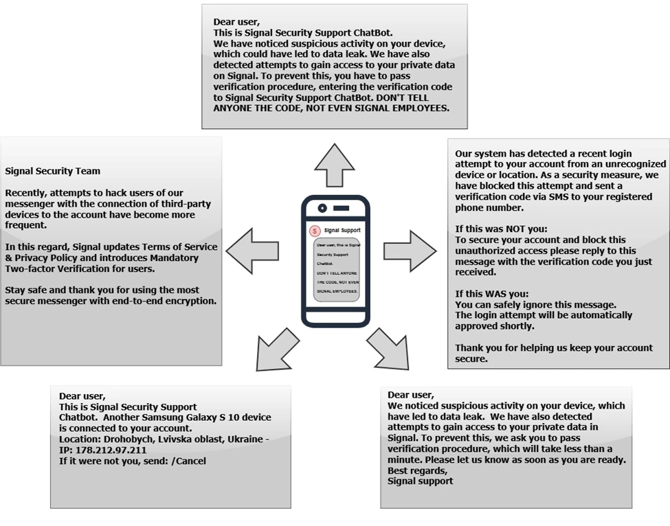
In some cases, attackers also exploited Signal’s linked device feature, sending malicious links or QR codes that allowed them to connect their own device to a victim’s account without taking it over completely.
Once an account was compromised, Russian spies were able to “view the victims' messages and contact lists, send messages, and conduct additional phishing against other Signal accounts.” The FBI warns that attackers may adjust their approach in the future to target additional messaging platforms or to directly install malware on users’ devices.
Preventing a phishing attack
Phishing remains one of the most common ways for hackers to gain illicit access to your accounts. These attacks may come through email, text, social media messages, or even phone calls. But in all cases, the process is the same – bad actors impersonate someone or something you trust to trick you into handing over sensitive information.
The FBI recommends vigilance as your primary defense. Treat unknown or unexpected messages with suspicion – if something feels off, pause before clicking any links or responding. And never share your PIN or 2FA codes for an action you did not initiate. Legitimate support services will not ask you to provide verification codes through messages within an app.
While there are multiple types of 2FA available, for accounts that require the highest level of protection using a physical security key or a passkey offers significant benefits over SMS codes. These methods only allow access to an account if you are in physical possession of the connected device, so there is no code or password for hackers to intercept.
Read more: How this security expert got phished – and why 2FA didn’t save him
[Image credit: FBI, CISA]
