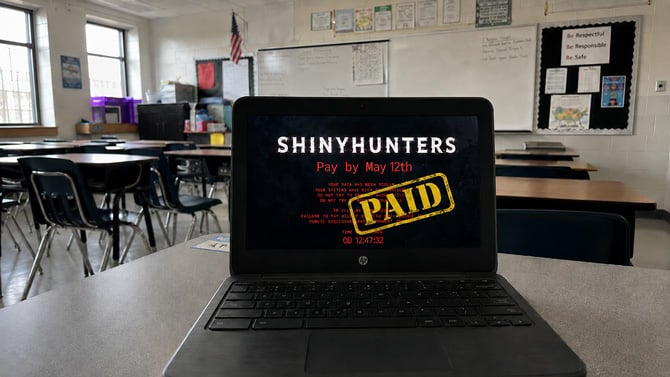
The company behind Canvas says it has reached an agreement with ShinyHunters, the hacking group that breached the educational platform used by more than 30 million students and teachers, and claims all stolen data has been returned and destroyed. Whether that's actually true is another matter.
Instructure posted a statement Monday saying it "reached an agreement with the unauthorized actor involved with this incident." According to the company, all data was returned, it received digital confirmation of data destruction, and it was told that "no Instructure customers will be extorted as a result of this incident, publicly or otherwise." A ShinyHunters representative told Reuters: "The data is deleted, gone. The company and its customers will not further be targeted or contacted for payment by us."
The representative declined to answer questions about the specifics of the agreement.
Ransomware negotiator Kurtis Minder told Reuters it's "fair to conclude that some money was sent." Instructure has not said whether it paid a ransom or how much. ShinyHunters had originally claimed to have stolen 3.65 terabytes of data, including names, email addresses, student ID numbers, and private messages, from nearly 9,000 schools worldwide. Instructure confirmed names, emails, IDs, and messages were exposed, and said passwords and financial data were not involved.
What the agreement actually covers
Instructure says the deal covers all affected institutions, and specifically advised customers not to reach out to ShinyHunters on their own. Reuters had reported Friday that individual schools were already contacting the group directly in an attempt to protect their own data. If you go that route now, Instructure is telling you not to – any contact with a criminal extortion group carries its own risks.
The more uncomfortable reality is that there is no way to independently verify that ShinyHunters deleted the data. The group operates on trust, which is a strange thing to extend to a criminal organization. Paying a ransom does not guarantee that copies weren't kept, shared, or sold before the deal was struck.
Congress wants answers
Also on Monday, the House Homeland Security Committee sent a letter to Instructure CEO Steve Daly requesting a briefing on the breach. The committee wants to know the full scope of what was stolen, how the company responded, and whether it properly coordinated with federal law enforcement and CISA, the Department of Homeland Security's cybersecurity agency. Instructure did not immediately respond to questions about the congressional request.
What you should do to stay protected
The agreement doesn't change the exposure that already happened. If your name, email, student ID, and private Canvas messages were among the stolen records, that information existed in ShinyHunters' hands for nearly two weeks. Even if the data was deleted, it's worth assuming it could still surface.
Be alert to phishing emails that reference Canvas or your school, or that use language that sounds like it came from a professor or administrator. Go directly to your school's portal rather than clicking email links. Change your Canvas password if your school uses direct login rather than single sign-on. If your child uses Canvas for K-12 schoolwork, apply the same steps to their account.
Check Instructure's status page for ongoing updates.
Read next: How to Tell if an Email Has Been Spoofed
[Image credit: Suzanne Kantra/Techlicious generated by ChatGPT]
