 Earlier this month, researchers announced Heartbleed, a serious Internet security vulnerability that went undetected for two years, possibly affecting an estimated 500,000 websites through which hackers could conceivably pilfer login information, credit card numbers and other data. As a result, security experts have widely recommended changing all your passwords for sites that have upgraded their security certificates.
Earlier this month, researchers announced Heartbleed, a serious Internet security vulnerability that went undetected for two years, possibly affecting an estimated 500,000 websites through which hackers could conceivably pilfer login information, credit card numbers and other data. As a result, security experts have widely recommended changing all your passwords for sites that have upgraded their security certificates.
But creating strong passwords is trickier than it used to be.
According to security expert Bruce Schneier, hackers are becoming increasingly adept at figuring out login credentials, thanks to fast and powerful computers running software that can crack encrypted passwords by guessing millions of variations per second.
Password crackers try common passwords like “letmein” with prefixes or suffixes such as “1” or “!” and run various dictionaries of English and foreign words and names along with appendages such as dates and replacing letters with symbols (such as “@” for “a”). These tactics are remarkably effective at breaking passwords and crack even those you’d think look pretty unguessable — passwords such as “k1araj0hns0n" and "Sh1a-labe0uf.”
So what’s the best way to create a strong password you can remember? Follow these tips to the best password practices.
1. Use a meaningful sentence
Schneier suggests turning a meaningful sentence into a password. For example, "This little piggy went to market" turns into "tlpWENT2m." Notice that not only does this password use the letters from the sentence, but it uses both uppercase and lowercase characters and replaces “to” with “2.”
2. Never reuse a password
It’s imperative that you never use the same password on more than one website.
“Even if you choose a secure password, the site it's for could leak it because of its own incompetence,” Schneier writes. “You don't want someone who gets your password for one application or site to be able to use it for another.”
 3. Use a password vault
3. Use a password vault
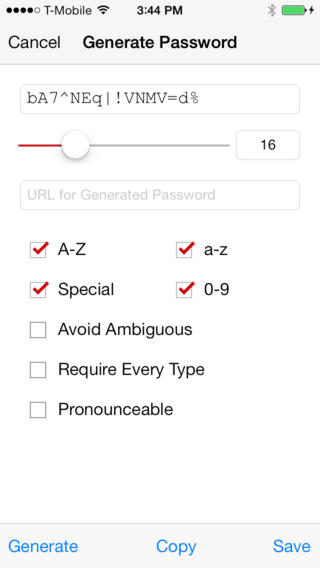
My favorite password vault is LastPass because it will generate unique passwords such as “R4fpo9)mswH” and saves them in an online vault. Even better, the LastPass browser extension automatically fills in login credentials on every site for which you’ve saved a username and password, so you don’t have to try to recall difficult-to-remember passwords.
For $12 a year, get LastPass on your mobile device so you can access your passwords when you’re not sitting at your computer. LastPass is available in the iTunes store, Google Play and the Windows Phone store.
LastPass's Security Check feature was recently updated to alert users to which of their accounts may have been compromised by Heartbleed, as well as the last time a site's password was updated and if the site has updated its certificates to make it safe from Heartbleed. Since LastPass is free to download to your computer, it’s a tool worth using. After downloading and installing LastPass, click the LastPass icon in your browser toolbar, then Tools menu, then Security Check.
4. Use two-factor authentication
Two-factor authentication adds an extra layer of security by asking for something else in addition to a password before allowing you into a website. Google and Facebook, for example, offer to text you a code that you have to enter on a login page. Google has a page explaining how to sign up for their two-factor authentication service. For Facebook, enable 'Login Approvals' from the 'Account Security' section of your account settings page.
5. Check every site you visit before creating a new strong password
Much of the Internet is still vulnerable to Heartbleed data leaks, so before you change a password on a site, check to see it has upgraded its security. A couple of new browser plug-ins make doing so easy: the Chromebleed extension for Google Chrome and the Heartbleed-Ext extension for Mozilla Firefox, both of which check for Heartbleed on every website you visit.
[women with tablet and credit card via Shutterstock]

From Michael White on February 02, 2015 :: 3:33 pm
How does Clef rate as an alternative to passwords ?
Reply
From Josh Kirschner on February 03, 2015 :: 3:24 am
Clef, and other two-factor authentication tools, are generally far safer than password-based applications. However, they are also harder to use. While I haven’t studied Clef in detail, it likely requires you to have your phone on you to log in (if your phone is out of batteries or lost, you’re out of luck). Plus, it may only work with sites that have Clef as a log in method (a very tiny number, I imagine), Then there is the issue that Clef is still a small startup. If they’re not around in six month, the app will stop working. That said, Clef does seem to be one of the better two-factor solutions I’ve seen.
Reply
From Michael White on February 03, 2015 :: 1:05 pm
Clef seems to be handled thru another 3rd party or applied source called Waltz, this can then be used on any website that requires a password, it can be an annoying little popup But again as you say unless you have your phone its useless although i think there is a work around that bypasses clef but then what is the point of it if there is a work around????
Reply
From Michael White on February 03, 2015 :: 1:06 pm
http://getwaltz.com/
Reply