 We absolutely despise adware here at Techlicious. As we’ve discussed before, a number of unsavory companies and hackers make their living inserting extra ads into the websites you visit. These ads are annoying to look at, clutter up your screen, seriously impact your phone or PC’s performance, gobble up data, interfere with existing website code, reduce your privacy and generally jeopardize the security of your device. They also harm the sites you’re visiting – especially those that are supported by their own ads. Google classifies most ad injectors as malware, and its Chrome division notes that it has received more complaints about ad injectors in 2015 than about any other issue.
We absolutely despise adware here at Techlicious. As we’ve discussed before, a number of unsavory companies and hackers make their living inserting extra ads into the websites you visit. These ads are annoying to look at, clutter up your screen, seriously impact your phone or PC’s performance, gobble up data, interfere with existing website code, reduce your privacy and generally jeopardize the security of your device. They also harm the sites you’re visiting – especially those that are supported by their own ads. Google classifies most ad injectors as malware, and its Chrome division notes that it has received more complaints about ad injectors in 2015 than about any other issue.
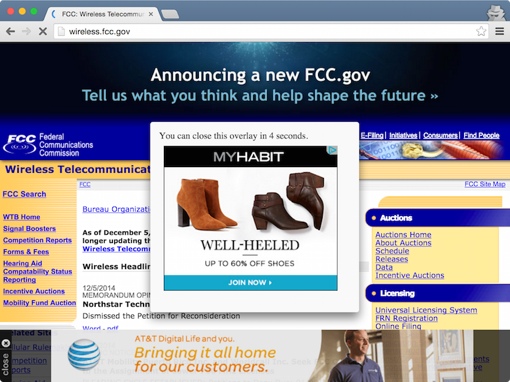
It’s a bit surprising, then, that AT&T has been caught red handed using this ad injector tech on its public hotspots. Stanford lawyer and computer scientist Jonathan Meyer yesterday noted on his Web Policy blog that, during a trip through the Washington Dulles International Airport in Virginia, he noticed that an AT&T hotspot was injecting obnoxious ads on all sites he visited. Some sites had overlay ads that can’t be dismissed until a countdown timer expires; other sites had added banner ads; many were saddled with both. Even government and non-profit websites were plastered with ads when Meyer visited. (No ads were delivered over HTTPS secure sites.)
Suspicious of all the ads, Meyer analyzed the HTML code of the pages he was being served and noticed that all had extra lines of code added by the AT&T hotspot. This exposed all his web traffic to a third party advertiser called RaGaPa, which almost certainly pays AT&T for the privilege. There is no disclaimer that the ads that pop up are a result of this AT&T/RaGaPa partnership, nor is there an element in the AT&T Wi-Fi terms of service to warn about the third-party data collection.
The best way to avoid these third-party ad injectors is to avoid these free AT&T hotspots when you can. Still, if the lure of free Internet is too great, there are a few things you can do to fight back against the ads. Connect to sites via a HTTPS secure connection when you can – third parties can’t intercept them. You should also try the new Privacy Badger browser extension – it blocks the flow of your data to advertisers. Be sure to check out our picks for the browser privacy tools (that don’t make life more difficult), too!
[Image credit: Jonathan Meyer]












