 Smartphone technology and the Internet have opened up countless new ways for us to interact, learn, play and communicate with each other. Unfortunately, it’s had a negative side effect, too: Just about everything we do now creates a trail. And as we’ve seen, the U.S. government and law enforcement love using that trail to catch criminals, regardless of whether doing so may violate our constitutional rights.
Smartphone technology and the Internet have opened up countless new ways for us to interact, learn, play and communicate with each other. Unfortunately, it’s had a negative side effect, too: Just about everything we do now creates a trail. And as we’ve seen, the U.S. government and law enforcement love using that trail to catch criminals, regardless of whether doing so may violate our constitutional rights.
One such tracking tool used by law enforcement, StingRay, has been getting a lot of attention in the news lately. It’s a small box that essentially acts as a fake cellphone tower (commonly called a “cell site simulator”). When a Stingray is activated, nearby phones are tricked into connecting to it, allowing the police to track the exact location of specific cellphone owners. Some models also allow the collection of metadata, such as specific phone numbers called.
It’s very possible, though, that StingRay could be a lot more powerful than even that. The Federal Bureau of Investigation has made a point of aggressively protecting Stingray technology through forced secrecy, preventing local law enforcement agents from answering questions about the tech, even under oath in court. “Disclosure of even minor details about the use of cell site simulators may reveal more information than their apparent insignificance suggests because, much like a jigsaw puzzle, each detail may aid in piecing together other bits of information even when the individual piece is not of obvious importance in itself,” said FBI Supervisory Special Agent Bradley Morrison in a sworn deposition last year (PDF). “While the product of the identification or location operation can be disclosed, neither details on the equipment’s operation nor the tradecraft involved in use of the equipment may be disclosed.”
But if the FBI’s goal here is to protect the public, forced silence over Stingray tech is having the exact opposite effect. As the Washington Post notes, Florida prosecutors decided to offer an armed robber 6 months’ probation rather than disclose details about cell site simulators in court. Similarly, St. Louis, Missouri prosecutors flat out dropped armed robbery charges against three defendents rather than talk about Stingray under oath. In Baltimore, prosecutors withdrew StingRay-obtained evidence in a robbery case instead of discussing details about how it was obtained. In Tacoma, Washington, hundreds of cases could now be at risk of being overturned after law enforcement officers misled judges about the use of the technology. And this, frighteningly enough, is only the tip of the iceberg.
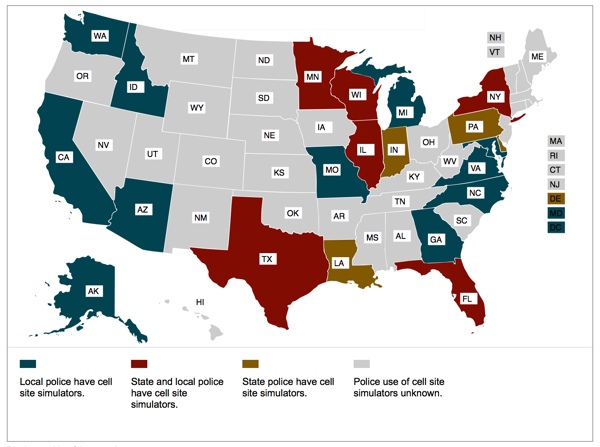
According to the American Civil Liberties Union (ACLU), cell site simulators are currently being used in at least 20 states. Due to the secrecy behind StingRays, it’s unknown whether police in the other states use the technology or not. The only real barrier to its use, it seems, is the $68,000 to $134,000 price tag of the device.
Aside from the damage that FBI secrecy is causing the prosecutors, there are significant privacy and constitutional questions about the use of StingRay. The FBI and local law enforcement are quick to point out that they only use the technology under court approval, but it appears there are many cases in which approval was not sought. And the requirement that law enforcement not discuss StingRay in court may very well be unconstitutional in and of itself.
Want to learn more about StingRay technology? Check out the ACLU’s report, which contains an interactive map detailing specific cases in your state involving the use of cell site simulators. You might also want to check out this week’s piece on StingRay at Vox, as well.
[Image credit: Harris; ACLU]














