 If you use Google Chrome and search for helpful extensions like AdBlock Plus or Instapaper, be careful, because Google’s search algorithms might inadvertently be leading you to install malicious apps instead.
If you use Google Chrome and search for helpful extensions like AdBlock Plus or Instapaper, be careful, because Google’s search algorithms might inadvertently be leading you to install malicious apps instead.
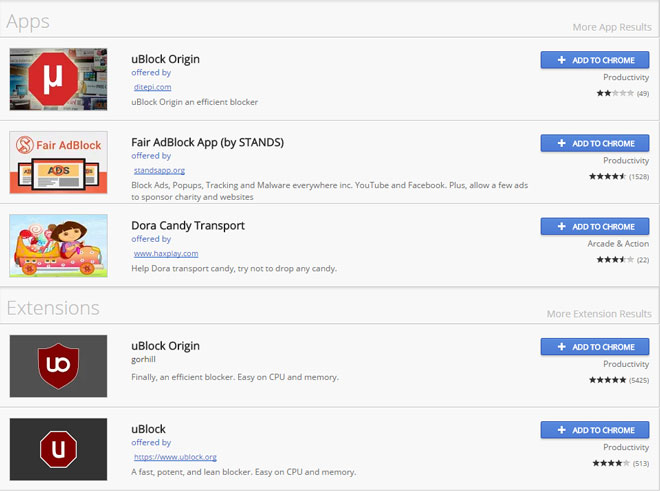
PCWorld’s Chris Hoffman first reported on the flaw, and it’s certainly caught our attention. Hoffman uses the example of ublock, one of the most popular adblocking extensions for Chrome. If you search “ublock” in the Google Web Store as we replicated in the image below, you see that Google lists Apps before Extensions, and there are a ton of both that look like the real thing, but are really just sneaky doppelgängers masquerading as the extension from the official ublock.org.
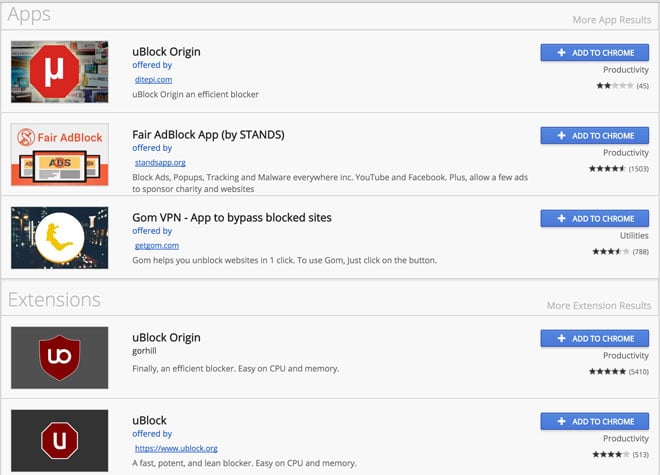
Hoffman says that these untrustworthy developers are exploiting a problem related to Google’s algorithm, which prioritizes and shows Apps before Extensions. He believes that Google is doing this because while Extensions are fairly popular, Chrome apps haven’t taken off.
Google’s power lies in the fact that they write the algorithms that lead to whatever they want them to lead to. This problem was illustrated in a 2015 study that showed that Google could even alter an election by changing the order of users’ search results. If you’re logged in to Chrome with your Google account, you might get different search results, as well. When I use Incognito Mode, my “ublock” results are different.
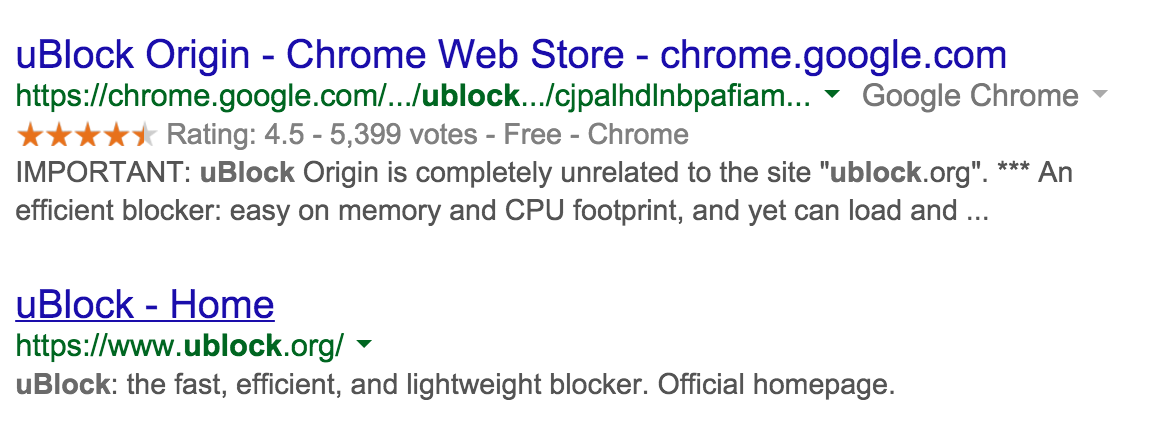
And searching for “ublock” using Google leads to the inauthentic app first, with a message saying “IMPORTANT: uBlock Origin is completely unrelated to the site “ublock.org”."
A subtle tweak in Google’s algorithms might be a solution to these problems. After all, when The Windows Store had a similar problem with deceptively named apps in 2014, they eventually removed 1,500 of these apps that they said were “trying to game the system with misleading titles or descriptions.”
Google could certainly take a page from Microsoft’s book and begin removing these less-than-above-board apps from the Chrome Web Store entirely. In addition, they should list the more popular Extensions before Apps in the Web Store, so people are less likely to be tricked into installing something that could steal and misuse their information.
If you want to see the Apps and Extensions are installed in your Chrome browser, type “chrome://apps” or “chrome://extensions” into the search bar. You may have accidentally downloaded one of these faux apps yourself. When installing new apps, you should always check the developer name and the reviews listed to make sure they’re legit. As shown above, straight Google searching the Extension or App might also show you which one is the real one.
Check out more tips for securing your online life here.
[Image credits: Google]

From Darren on February 05, 2016 :: 5:16 am
This article is saying that searching for ublock on the chrome store will show you apps called ublock but are not from the same people as ublock.org…
But, what exactly does the ‘malicious’ Ublock Origin app do to harms or negatively effect the PC/Chromebook that you’ve installed it onto?
If the software works… Does it matter that its ripped off the name (from our point of view as the users)
Reply