We are what we browse, at least online. As our lives and movement become increasingly documented thanks to smartwatches, smart cars and smart homes, the amount of data we are generating is skyrocketing, but our control over its use is diminishing.
Fortunately, you can take steps to keep control over your increasingly valuable data. Just as crucial, your efforts help set precedents for how companies and lawmakers can use what will be an exponentially growing mountain of sensitive personal information in decades to come.
1. Use HTTPS Everywhere
The HTTPS Everywhere browser plug-in (for Chrome, Firefox, Opera and Firefox for Android) from the privacy group Electronic Frontier Foundation ensures that your connection to sites is encrypted, at least at sites that support the HTTPS protocol, so that snoops can’t view what you’re doing on the site. Your ISP can still log the fact that you visited that site.
2. Use virtual private networks
A virtual private network (VPN) can mask your IP address, a main identifier of your computer or phone, so that ad trackers and your ISP can’t see what sites you visit or your activity there. That makes it handy for safely using public Wi-Fi networks, too.
VPNs do this by encrypting your internet traffic, passing it through its own servers before sending it to your destination site. This adds another layer to your privacy issues: you now also need to trust your VPN provider, because it can see all your traffic. Though there are some reputable VNP providers that provide a free version of their VPN, a good rule of thumb is to choose a paid VPN service, which reduces the financial incentive to sell details about your online activity to advertisers.
NordVPN

This über-secure service encrypts all data twice, doesn’t log activity and can route traffic through servers in 59 countries on every continent except Antarctica. To create browsing that is anonymous and private, it can send traffic from its servers through the Tor network, which further scrambles the data so it reaches its destination with the IP address of a random computer in the Tor network. One subscription works for up to six devices, including iOS and Android devices.
Price: starting at $2.99/month (for a 3-year subscription) or $11.95/month at NordVPN
TunnelBear
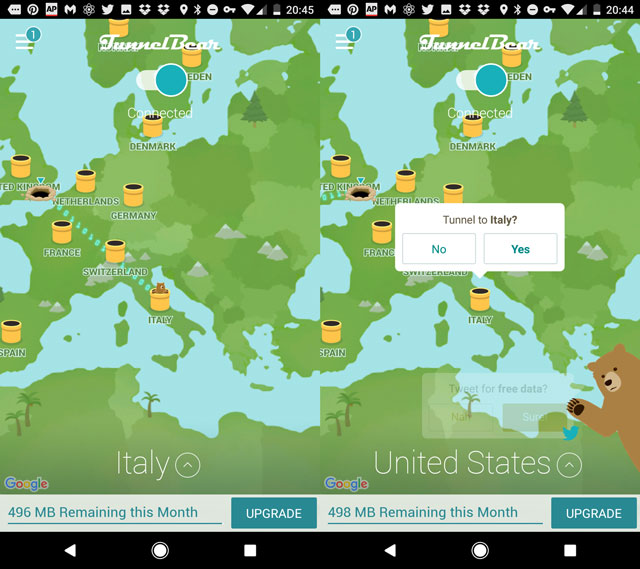
Via the über-cute design flourish of a bear who pops up in tunnels across the world in the name of encrypting your internet traffic, TunnelBear offers unlimited data and bandwidth. Use up to five connections for your computer (Windows PC or Mac) as well as iOS or Android tablet, phone and other devices. TunnelBear has a no-logging policy for all activity. Choose to appear to be from over 20 countries in five continents. If you need to visit a government or website that blocks VPN traffic, try the GhostBear feature, which scrambles the encrypted traffic and makes your VPN use harder to detect.
Price: $4.99/month (paid annually) or $9.99/month; free version with 500MB data per month at TunnelBear
3. Use a secure browser
There are quite a few ways to browse anonymous9ly, such as installing anti-tracking plug-ins and clearing cookies in order to dissociate browsing sessions from each other. But if you’re willing to give up the comfort of your favorite major-league browser, a privacy-centric browser can accomplish all of the above in one handy package.
Epic
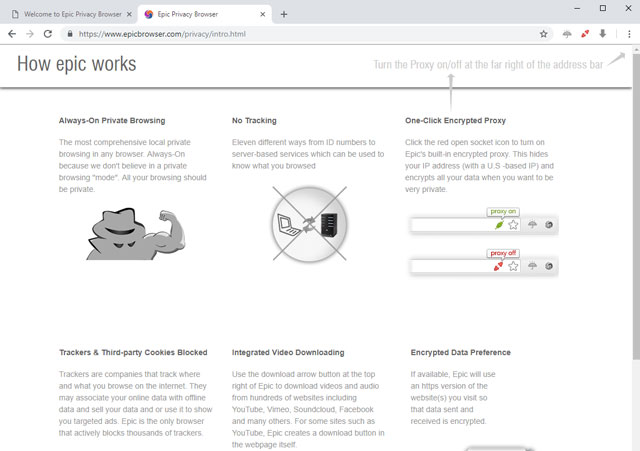
Built on the same core as Google’s Chrome browser, the minimal Epic Privacy Browser blocks several types of tracking, with a fascinating counter of just how many trackers it has blocked on other browsers on the same computer. A built-in proxy network feature reroutes your traffic through U.S.-based servers so that your IP address appears different every session, preventing the accumulation of a profile associated with your computer’s real IP, whether via site visits or search queries. If a site supports HTTPS, Epic always connects via this encrypted protocol.
Price: Free on EpicBrowser for Windows PCs and Macs
Ghostery
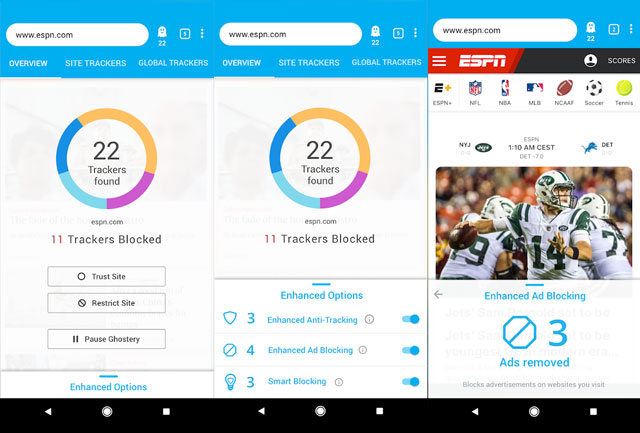
Protect your mobile browsing by using the tracker-blocking browser Ghostery, which is also available as a plug-in for desktop browsers. Because the default search engine is Google, to avoid allowing the Big G to tie your search queries to your phone’s ID, hit up a more privacy-focused search engine (see below), or head into your Google Account settings to delete your search history. Ghostery also has a handy setting to automatically request desktop versions of sites.
Price: Free on Ghostery for Windows PCs, Macs, iOS devices and Android devices
4. Use a secure search engine
What we search for doesn’t just yank the curtain back on a host of revealing details, ranging from impending pregnancy to mental health patterns—over time, our search queries can also influence the results we’re shown. Three quarters of U.S. searches are made via Google, which tracks what you search for and click on in order to fine-tune what you’re shown in the future. You can turn off Google’s personalized search (at Search Tools > All Results > Verbatim) but that doesn’t stop your searches being saved. Instead, consider using a privacy-focused search engine.
DuckDuckGo
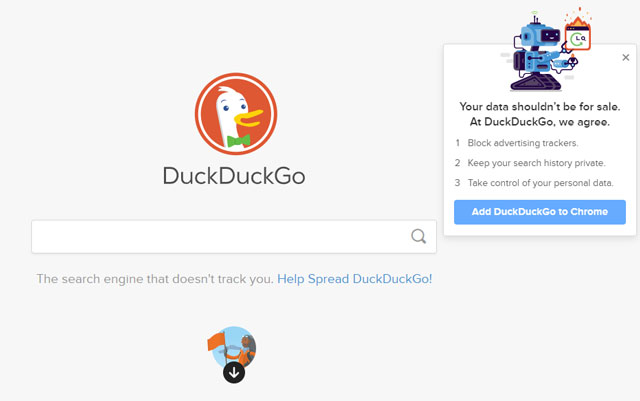
Sleek and fast, the DuckDuckGo search engine doesn’t save search history, track users or collect personal information from your computer. It offers many of the convenient features found in Google search, such as “zero-click info” that allows you to type simple queries such as “weather in Vegas” or “50 USD in euros” for an instant display of the results.
Price: Free at DuckDuckGo.com
Qwant
The France-based Qwant is a search engine with extras. Along with a fast search, its home page also displays trending news topics and videos. Search results display in a slightly cluttered view that shows news results plus results from Twitter, with image results laid out across the top.
Price: Free at Qwant.com
5. Use a secure messaging app
Not all messaging apps are created equal. You probably won’t be surprised to learn that Facebook Messenger isn’t the most secure way to communicate. But Apple’s iMessage is, because it uses end-to-end encryption so messages can’t be spied on in transit or at their destination or origin servers. And standard text messages, which are send over your carrier’s networks, are not encrypted at all.
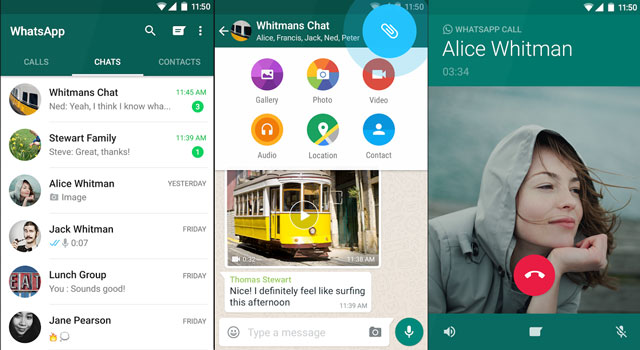
With 1.2 billion active users, WhatsApp is a great combination of security — it’s end-to-end encrypted — and convenience. Chances are, your friends are using it, too, and unlike iMessage, they don’t need to be Apple users. Secure communication only works if both parties are using an encrypted app. Bonus: Chatting on the web version, which sends messages through the phone app, is equally secure.
Price: Free from WhatsApp for Windows PCs, Macs, iOS devices and Android devices
Signal
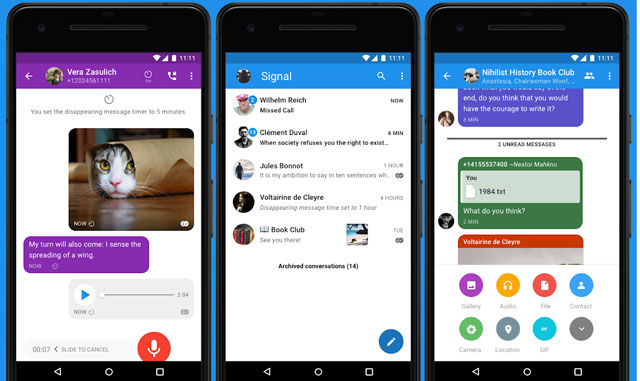
Like WhatsApp, Signal offers end-to-end encryption on all text and multimedia sent in all individual and group chats. Additional privacy features include locking the app and messages with a pass phrase, blocking chat screenshots and an option to relay calls through its servers to mask your IP address. Signal can copy your existing text messages into its encrypted database, which is handy if you want to shift from unsecured comms without losing your text history.
Price: Free from Signal for Windows PCs, Macs, iOS devices, Android devices
6. Use a secure email app
Google recently stopped scanning Gmail messages for keywords for targeting advertising, but like most other email services, it does not offer end-to-end encryption of emails. Snoops including governments, businesses and hackers can still lift information from Gmail messages in transit.
Tutanota
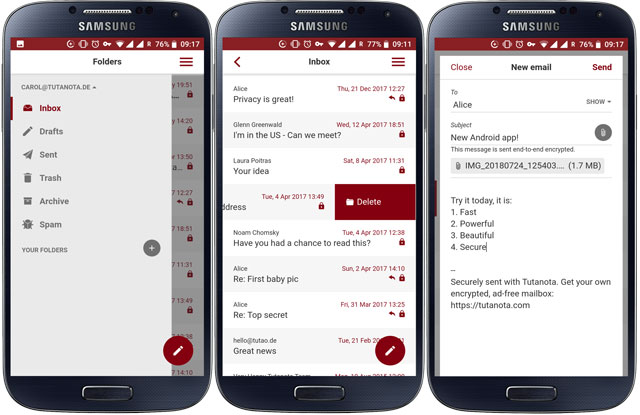
If the U.S. record of privacy law rollbacks has you glancing over your shoulder, the Germany-based, open-source Tutanota email app could be a good encrypted alternative to your current email provider. It encrypts your contacts list as well as your emails. Tutanota offers 1GB of mail storage for free accounts and allows password-protected emails to non-Tutanota users.
Price: Free or $1.35/month for premium, with ability to use own domain, at Tutanota for Windows PCs, Macs, iOS devices, Android devices
ProtonMail
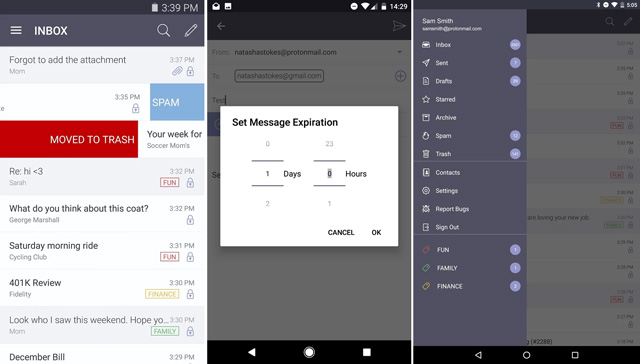
ProtonMail email service, designed by CERN scientists, has servers in Switzerland and uses end-to-end encryption. Messages cannot be read by anyone, including ProtonMail itself. Messages can be set to self-destruct after a set period. Upgrading to the premium version allows you to send end-to-end encrypted emails to non-ProtonMail users.
Price: Free or from $5/month for premium from ProtonMail for Web, iOS devices, Android devices
7. Use a password manager
One of the most basic ways to protect sensitive personal data is to put a strong password on all your accounts, including the email app you use every day and the shopping accounts you opened years ago. The breach of a single account with an easy-to-crack password can reveal innocuous data such as your birthday or hometown, which can then be used to hack more lucrative accounts.
Since most of us use dozens of accounts and apps, a password manager is the easiest way to store — and just as important, to create — unique, tough-to-crack passwords for every account.
Dashlane
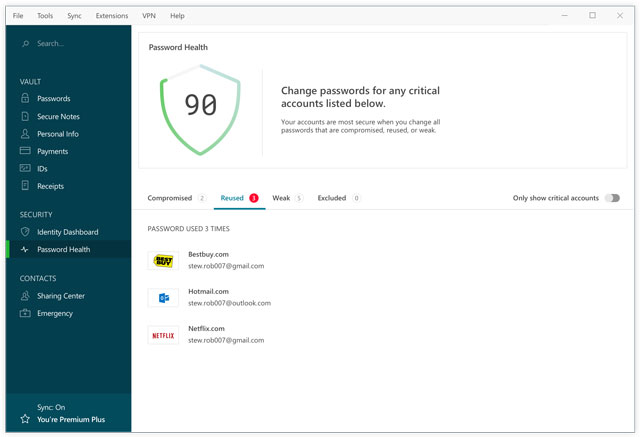
This easy-to-use app imports passwords your browser has saved into its encrypted vault. It can run a health check to flag weak or recycled passwords. If you go for the paid subscription, Dashlane will come up with new, unique and strong passwords for old and new accounts. You’ll also be able to use Dashlane to log in on multiple devices (premium service required). And with the Dashlane app for Android and iOS, you can used user names and passwords stored in the app to log into site and apps — no retyping or copying and pasting necessary. The app has a secure notes section to encrypt sensitive information such as financial details. And, the Premium subscription comes with VPN service.
Price: Free or $4.99/month billed annually for premium, at Dashlane for Windows PCs, Macs, iOS devices, Android devices
8. Use an anti-malware program
All the security apps on this list can’t help if a snoop is able to access your personal info at its core: your computer. Viruses or other malware, which may be downloaded via phishing emails or malicious sites, can wreak damage by copying sensitive financial details, spying on online activity, or tracking keystrokes to log passwords. A solid anti-malware program is the foundation of your digital security, with the ability to block spam and phishing sites, stop viruses before they get a foothold, and paid-for versions often also include a password manager and additional encryption for financial data.
Bitdefender Total Security 2019
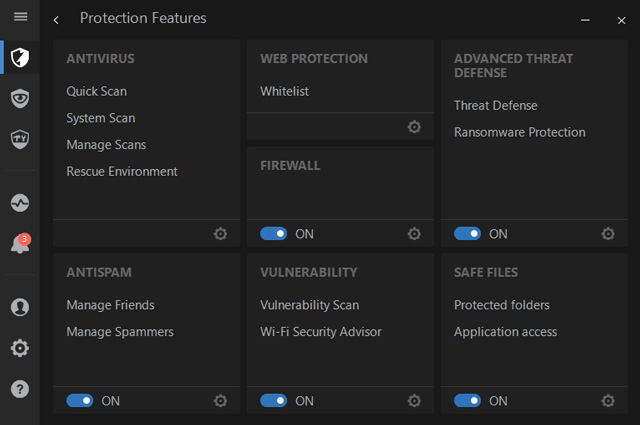
This all-round program blocked 100% of widespread malware and “zero-day attacks”, and had one of the lowest impact on computer performance in tests by industry benchmarker AV-Test. It also warns of potentially malicious sites, scans emails for malware, and additionally offers protection features including a password manager, encrypted banking and shopping transactions, and data backup to a secure cloud. (Need fewer features? You can also install the free version, Bitdefender Antivirus Free Edition.)
Price: $44.99 on Bitdefender (check price on Amazon) for up to five devices, including Windows PCs, Macs, iOS devices and Android devices
[Image credit: woman surprised looking at smartphone via Shutterstock, Nord VPN, Tunnel Bear, Epic, Ghostery, DuckDuckGo, Qwant, WhatsApp, Signal, Tutanota, ProtonMail, Dashlane, Bitdefender]
Updated on 5/31/2019

From xian on July 26, 2017 :: 12:57 pm
burnerapp to protect your number, proton mail to secure your mail, ivacy to protect your data and encrypt it and whatsapp for end to end encryption messages. for password management, passpack is a great add
Reply