We may earn commissions when you buy from links on our site. Why you can trust us.
Mobile Security Apps Perform Dismally against Spyware
Mobile spyware can have a devastating effect on your life; the constant fear that a spouse, significant other or even employer is following your every move, knows everything about your life and has completely removed any vestige of privacy. (If you have any doubt about this, read the comments from readers from our March 2012 story on mobile spyware).
And spyware is not as rare as you may think. According to mobile security company Lookout, .24% of Android phones they scanned in the U.S. had surveillance-ware installed intended to target a specific individual. Sophos reports a similar .2% infection rate from spyware. If those numbers hold true for Android users in general, that would mean tens of thousands could be infected.
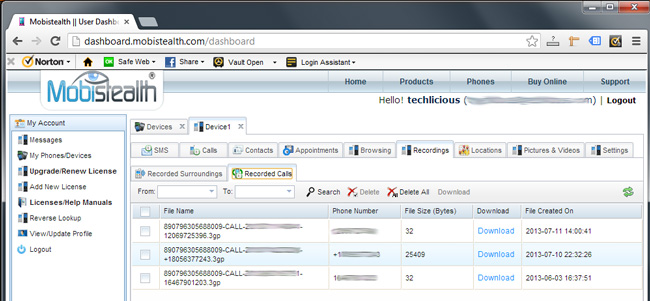
I set out to test the leading Android anti-malware vendors to see how they fared at protecting us against the threat of spyware. Spyware apps I used for this test go far beyond basic location trackers or “find my phone” services. While features varied, all the apps I tested performed a combination of highly intrusive monitoring techniques, including recording of calls, remote camera image capture, downloading of SMS messages, downloading of photos and videos, downloading of contacts, remote microphone activation, and recording and tracking of websites visited. You can find out more about how I define spyware, how I picked the spyware apps and how I tested in the FAQ below.
The results, generally speaking, were dismal. Of twelve products I tested, none was able to detect more than two-thirds of the samples. Many missed half or more of the spyware apps. And, surprisingly, the potential spyware apps least likely to be detected were those widely available in Google Play.
And this isn’t just an Android issue. I was able to easily install spyware on an iPhone 3GS, with essentially the same functions as on an Android phone. The only difference between the iOS process and that of Android was that I was required to jailbreak the iPhone (modifying the operating system to get past the built-in security controls) first. Nonetheless, the full process took less than an hour.
I was unable to test anti-malware for iOS devices because there isn't any; Apple’s restrictions on what apps sold within iTunes can do prevents effective anti-malware products. However, the iOS app from Lookout did warn that the iPhone was jailbroken—a pretty clear indicator something may be up with your phone.
BlackBerries using operating systems older than BB10 are susceptible to the same spying risks. I successfully ran Mobistealth on a BlackBerry Torch and the (very) limited security choices available in BlackBerry World—NQ Mobile and McAfee—were unable to detect it.
Read my recommendations below for advice on how to protect yourself.
Summary of the results
Across the board, overall performance was far lower than I expected. The best anti-malware applications in our testing (Avast Mobile Security, Norton Mobile Security, Trend Micro Mobile Security, and TrustGo Security) only picked up six of our nine samples, a 66% detection rate. In any other malware detection testing, this would be considered dismal. The worst (ESET Mobile Security and NQ Mobile) only caught three of the nine, a 33% detection rate. Kaspersky Mobile Security, McAfee Antivirus & Security, and Sophos Security fell in the middle of the pack.
[UPDATE 9/24/15: TrustGo Security appears to no longer be in business. While the app is still available in Google Play, you should not download it as neither the app nor malware definitions are being kept up to date.]
While it’s difficult to make statistical conclusions for how these programs would fair against a larger sample of spyware apps, the fact is the spyware apps tested should have been easy hits for the security companies. Each has been around for quite some time (years in many cases), and has either been reported in the media or is easily available via a Google Search. Plus, each app tested was already flagged by at least one security vendor as malware. And, counter-intuitively, the spyware apps that were most likely to be missed were those that are either currently available in Google Play or were in the past.
So why the poor showing? I spoke to representatives from half of the anti-malware companies included in the test and there seems to be a fundamental disconnect between how they identify which apps categories to focus on and where the real risks lie for U.S. smartphone owners.
First, there seems to a strong bias by security vendors (especially those based outside the U.S.) towards focusing on apps that are available through foreign app markets, where many of the newest malware risks originate. The problem is that most U.S. smartphone owners are unlikely to download an app from a Russian or Chinese app store, so covering these apps does little to protect us. And since spyware programs are usually downloaded directly from individual vendors, not through an app store, these products are missed entirely by many security vendors.
Second, security companies are not capturing as many spyware risks as they should because of their philosophy of classifying this type of software as “Potentially Unwanted Apps” (PUA). Since, the argument goes, PUAs require someone to manually install it and agree to the terms, and since PUAs could have (legally) valid uses, such as parental tracking, employee monitoring (with, presumably, informed consent) or tracking down a phone thief, these apps are not included in the threat databases, regardless of how dangerous they could be in the wrong hands. The presumption of valid use is a major pitfall to proper detection of threats. And more than one security company told me they also had liability concerns about identifying PUAs as “malware”—instead waiting for Google or another security company to take the first step in classifying the app before they did so as well.
A more robust approach for security companies would be to identify PUAs during scans as potential malware so users can make their own determination about whether the app is wanted or not.
I spoke to many of the security vendors after the testing about the results for their product. Reactions were mixed. Most I spoke with showed a desire to develop a more robust methodology. Others, clung to the notion that potentially legitimate apps should not generate warnings—hopefully, shedding some sunlight on this topic will cause them to reconsider their position.
Why my test results are different than other anti-malware tests
Many of the anti-malware programs performed well in overall anti-malware testing from anti-malware testing lab AV-TEST, yet did poorly in my spyware-specific tests. How did these programs get such high detection rates when they seemed to be largely ignoring the spyware threat?
The reason became obvious when I looked more deeply into the methodology. AV-TEST, one of the most well-known testers of anti-malware solutions, only tests Android security programs with “malicious apps discovered in the last 4 weeks.” The spyware apps I tested have been available for months or years.
I reached out to AV-TEST to get the rationale behind the methodology.
According to Maik Morgenstern, Chief Technology Officer of AV-TEST, “Android malware is very short-lived. If malware makes it for example into the Google Play Store it will usually be removed after a few days. Also if an anti-virus vendor detects a certain malware sample, it is usually shared with other vendors so that in a few days most users are protected from this malware sample...So testing [old malware] would give a false impression of the real protection level, where protecting against relatively new samples counts."
Obviously, this did not match what we saw with our spyware testing, so I asked him how AV-TEST handles spyware, specifically.
“PUA/PUP/Adware/Spyware whatever you call it, is another story. Some vendors decided to not detect those as they are not necessarily a threat...The question is where do these apps cross the line? And this is very difficult to say. Therefore we are testing against PUA/PUP in our tests but don't publish the results until a consensus has been reached in the industry. Else we would hurt certain vendors that deliberately decided to not detect those apps for good reasons.”
In short, the industry is broken when it comes to spyware. Because security vendors can’t agree to classify spyware as malware, testing organizations ignore it in their evaluations. The result – protection rankings that don't reflect the true risks faced by U.S. mobile phone users. It’s time for the industry to take a stand and agree that apps that can be used to intrude your privacy should be identified in malware testing, even if they may have legitimate uses, as well.
Recommendation for smartphone owners
To keep your phone from being compromised, always use a strong password on your lock screen (one that a potential spy close to you wouldn't guess). It’s also helpful to check to see if you have USB Debugging Mode turned on in Android (it’s off by default), which would allow someone to bypass the lock screen to install apps. If it’s on, that’s a bad sign, and you should turn it back off or do a factory reset of your device.
Given the poor showing from all of the anti-malware vendors, Android owners concerned about spyware on their phones should use a combination of security apps to scan. I would recommend Webroot SecureAnywhere, which did a better job than most at finding spyware apps from Google Play (though it did a poor job elsewhere), plus either Avast! Mobile Security, Norton Mobile Security or TrustGo Security. For the purposes of spyware detection, paid apps showed no benefit over free apps (and, in general, actually performed worse).
While there is no way for iPhone owners to directly scan for spyware, installing spyware on an iPhone requires the phone to be jailbroken. So a security app like Lookout Security that warns if your iPhone is jailbroken will do the trick. A jailbroken iPhone can be fixed by upgrading to the latest iOS release.
[UPDATE 12/16/14: since this article was written, certain holes were identified in iOS that exploit the iPhone's connection to trusted networks and devices to allow someone with access to the network or device to download significant amounts of personal data. Jailbreaking the iPhone was not required. Fortunately, those holes have been patched in iOS 8. For more information, see: http://www.zdziarski.com/blog/?p=3820]
BlackBerry owners are mostly out of luck. Your best bet if you suspect you are being spied on is to do a factory reset of your phone.
I didn't test Windows Phone because of the very low ownership rate and, fortunately for Windows 7 & Windows 8 phone owners, difficulty finding spyware apps to test. Similar to BlackBerry, if you strongly suspect your Windows phone may have been compromised, a factory reset will likely resolve the issue.
Detailed testing results
The following nine applications that have the potential to be used as spyware were tested. The chart lists the commercial name, the app name that will appear in the running apps list and whether or not the app is available through Google Play (or, to the best of my knowledge, was formerly available).
| Commercial name | Application name | Google Play? |
|---|---|---|
| Kidlogger | Kidlogger | No |
| Mobile Spy | SIM Toolkit | No |
| Mobistealth | Lookout Secur | No |
| MobiUcare | MobiUcare | Yes |
| PDA Spy | Zend Setup, Invisible | Formerly |
| Phone Control | Android Manager | Formerly |
| SMS Tracker | SMS Tracker | Yes |
| Spytic | com.android, preference.help | No |
| Theftspy | Android Framework | Formerly |
Avast! Mobile Security
Hit rate: 6 of 9
Allows ignore: No
Spyware detected: Kidlogger, Mobile Spy, Mobistealth, PDA Spy, Phone Control, Spytic
Spyware missed: MobiUcare, SMS Tracker, Theftspy
AVG Antivirus Security
Hit rate: 5 of 9
Allows ignore: Yes, with no “unignore”
Spyware detected: Kidlogger, Mobistealth, PDA Spy, Phone Control, Spytic
Spyware missed: Mobile Spy, MobiUcare, SMS Tracker, Theftspy
Bitdefender Mobile Security
Hit rate: 4 of 9
Allows ignore: No
Spyware detected: Kidlogger, Mobistealth, PDA Spy, Spytic
Spyware missed: Mobile Spy, MobiUcare, Phone Control, SMS Tracker, Theftspy
Eset Mobile Security
Hit rate: 3 of 9
Allows ignore: No
Spyware detected: Kidlogger, PDA Spy, Spytic
Spyware missed: Mobile Spy, Mobistealth, MobiUcare, Phone Control, SMS Tracker, Theftspy
Kaspersky Mobile Security
Hit rate: 4 of 9
Allows ignore: No
Spyware detected: Kidlogger, PDA Spy, Spytic, Theftspy
Spyware missed: Mobile Spy, Mobistealth, MobiUcare, Phone Control, SMS Tracker
Lookout Security & Antivirus
Hit rate: 6 of 9*
Allows ignore: Yes, but shows message and user can see ignored app list
Spyware detected: Kidlogger, Mobile Spy*, Mobistealth , PDA Spy, Phone Control, Spytic
Spyware missed: MobiUcare, SMS Tracker, Theftspy
Special notes: Mobile Spy was missed in our first round of testing, but picked up in our second round. This was after I had discussed initial results with Lookout and mentioned Mobile Spy as one of the tested apps (we only discussed three of the nine), so it’s possible Lookout added the protection as a result of our conversation.
McAfee Antivirus & Security
Hit rate: 4 of 9
Allows ignore: No
Spyware detected: Kidlogger, PDA Spy, Phone Control, Spytic
Spyware missed: Mobile Spy, Mobistealth, MobiUcare, SMS Tracker, Theftspy
Norton Mobile Security
Hit rate: 6 of 9*
Allows ignore: No
Spyware detected: Kidlogger, Mobile Spy, Mobistealth*, PDA Spy, Phone Control, Spytic
Spyware missed: MobiUcare, SMS Tracker, Theftspy
Special notes: I discussed this story with Norton prior to commencing and mentioned Mobistealth as one of the apps to be tested.
NQ Mobile
Hit rate: 3 of 9
Allows ignore: No
Spyware detected: Kidlogger, Mobistealth , SMS Tracker
Spyware missed: Mobile Spy, MobiUcare, PDA Spy, Phone Control, Spytic, Theftspy
Sophos Security
Hit rate: 5 of 9*
Allows ignore: Yes.
No indication apps have been ignored. Ignore reset buried in separate menu.
Spyware detected: Kidlogger*, PDA Spy*, Phone Control, Spytic, Theftspy*
Spyware missed: Mobile Spy*, Mobistealth, MobiUcare, SMS Tracker
Special notes: Sophos provided a list of spyware apps (but not the underlying apk) to help us identify apps for this story (indicated with *). One they provided, Mobile Spy, was actually not picked up by their scan. This may be due to two spyware apps sharing a similar name or Sophos detecting an earlier version.
Trend Micro Mobile Security
Hit rate: 6 of 9
Allows ignore: No
Spyware detected: Kidlogger, Mobistealth, PDA Spy, Phone Control, Spytic, Theftspy
Spyware missed: Mobile Spy, MobiUcare, SMS Tracker
TrustGo Security (9/24/15: No longer operating - do not download)
Hit rate: 6 of 9
Allows ignore: Yes. Ignored apps buried in separate menu
Spyware detected: Kidlogger, Mobile Spy, Mobistealth, PDA Spy, Phone Control, Spytic
Spyware missed: MobiUcare, SMS Tracker, Theftspy
Webroot SecureAnywhere
Hit rate: 5 of 9
Allows ignore: Yes. Ignored apps buried in separate menu
Spyware detected: Kidlogger, Mobistealth, MobiUcare, SMS Tracker, PDA Spy
Spyware missed: Mobile Spy, Phone Control, Spytic, Theftspy
FAQs
How I define "Spyware"
For my study, I chose to define spyware as apps which capture significant information about an individual that could be used for tracking, monitoring and…well…spying. All of the apps I tested could be remotely controlled by a third party and deliver purloined content to them via a web interface, email or text message.
Just to be clear, these surveillance apps go far beyond basic location trackers or “find my phone” services. While features varied, all the apps I tested performed highly intrusive monitoring, including recording of calls, remote camera image capture, downloading of SMS messages, downloading of photos and videos, downloading of contacts, remote microphone activation, and recording and tracking of websites visited. With the exception of email access, which I wasn’t able to get working with the Nexus 4 I used for testing (though it may work on other devices), a potential spy could monitor every means of personal communication on your device, track your exact location at any time and even listen to your offline conversations. (See Android Spyware Apps: How Dangerous Are They? for additional details on monitoring capabilities)
That is some very, very scary stuff.
Spyware apps, not surprisingly, also do an excellent job at hiding themselves. Most showed no icon on the list of phone apps. The only way to find them was to look in the list of running apps within the Android settings menu. Even there, the apps often attempted to disguise themselves with names that sounded like system processes (e.g., Android Manager, SIM Toolkit, Android Framework) or security services (LookOutSecure).
Some security vendors I spoke with objected to the inclusion of apps such as MobiUcare (available in Google Play) in the test group on the grounds they are intended for the legitimate purpose of finding a lost or stolen phone. And they're right – MobiUcare could be used for legitimate purposes. However, its ability to track location, remotely record audio and take photos without the user being aware, and hide the app icon from the app drawer also make it a candidate for malicious spying.
It is important to note that all of the spyware I tested required someone to have physical access to your phone to install it. While this may make spyware seem to be less of a threat than malware that comes in the form of bad apps you download from an app market, it also reflects the deeply personal nature of the invasion, as someone close to you must be the perpetrator.
How I picked what potential Spyware to test
Since there is no comprehensive database of spyware apps (in fact, there’s not even agreement among the security vendors how to define “spyware”), I decided to use a “real-case scenario” approach to identify the apps for my testing. I took the perspective of a would-be spy and searched for apps using Google search, stories about spyware that had appeared in various media publications and searching the Google Play market. Using this approach quickly turned up a core group of apps for testing.
I supplemented my list with a sample of additional spyware apps identified by Sophos and Lookout. Since including these apps potentially biases the results in favor of those vendors, I indicate in the detailed results where a tested app was identified by the company.
In all, I tested nine apps that met my criteria for potential spyware: Kidlogger, Mobilespy, Mobistealth, MobiUcare Phone Locator, PDA Spy, Phone Control, SMS Tracker, Spytic, and Theftspy.
How I tested
For testing on Android, I used a stock Google Nexus 4 running Android 4.2.2. I changed the security settings to allow installation of apps from unknown sources, but did not root the phone.
Each piece of tested malware was loaded onto the phone and then run against each of the anti-malware solutions. When the anti-malware app gave me a choice, I always ran a “full” scan and checked boxes to scan for Potentially Unwanted Apps (PUAs). I scored the scan as a success if the anti-malware flagged the spyware as malware, PUA or similar designation. Since many of the detected spyware apps were classified as “PUA”, offering users the option to ignore PUA apps seems highly unwise. It would be far better to identify the apps and give users the option to “ignore” them individually.
I also note in the testing when the anti-malware app allows you to “ignore” identified risks and how those ignored apps are displayed in future scans. When it comes to spyware, the ability to ignore risks creates a huge potential hole for spies to hide their activities. If you have existing security software on your phone, the spy could ignore any warning during the spyware install process, effectively hiding the risk from future scans and giving you a false sense of security. One program I tested, AVG Antivirus Security gave no indication a risk had been ignored and no obvious way to see or reset the ignore list. Other apps, such as Sophos, TrustGo and Webroot, bury the ignored risks in separate menus that average users could easily miss. Of those programs that allow ignoring risks, only Lookout handled the process properly, clearly showing in the scan results both found risks and ignored risks.
I used the free version of the anti-malware apps for the testing unless the paid version offered additional protection features. Though each of the apps offers a wide variety of features, the scope of the testing was purely to focus on the spyware detection capabilities.
Discussion 
Excellent post! I noticed this the minute Android phones came out and did everything to avoid having to purchase or use one. Conspiracy theories aside, the phone I was previously using unexpectedly got zapped and stopped working. I swapped and activated one of the Android phones that I purchased on sale. As you mentioned with the defaults, I immediately noticed messages and calls being delayed. The phone would not ring or would immediately go to voicemail. While on a call, the line would open and go to speakerphone. So when calls were not showing up in my call log, I just disabled everything I could on the phone and still keep it working. I just need the phone to ring or dial.
The sad part is that all of this is built into the phone as a default which allows mobile savvy individuals to wreak havoc with unsuspecting cell phone users. Even worse, as stated, apps can come from anyone from anywhere. Most users trust that whatever is being installed and downloaded on their phone is reputable and will not invade their privacy. However every app I’ve seen or anything associated with Google always has a disclaimer to have access to all of your personal information.
Again, you mentioned that a number of apps that pretend to protect your identity and block spyware, actually does the same thing they claim to protect you from. It’s annoying, but expected. The only way to have true privacy is to not use technology, dig a hole in the ground and hide. Let’s not mention the RFID’s. Thanks for a great post and I’ll see about reactivating my first cell phone from the 90’s.
This proved that avast! Free Mobile Security gave you the best protection and, it’s totally free.
It is also highly regarded by AV comparatives and many publications.
Please remember that there is no such thing as a perfect AV. The virus always comes first and the method of protecting you against this new Malware doesn’t happen till the guys in the virus lab have figured out what makes this new beast tick.
My testing definitely showed there was no benefit to paid apps as far as spyware detection goes. Though I’m not willing to give any of the vendors a pass for the misses (including Avast!) based on the novelty of the threats. The spyware apps I tested have all been available for quite some time. The security vendors simply haven’t focused the attention necessary on this category to ensure users are properly protected.
Unfortunately, AV Comparatives does not provide enough detail into their methodology to determine whether spyware was included or not. Though, based on what they do say, I suspect it was not.
my friend has a wife that has hacked his phone and completely set him up into false criminal charges. the cops will not help him at all what she he do? if you want more details i will be glad to say more but i do not want to waste anyone’s time.Can she be caught?
If someone (like your wife) has physical access to your phone (or other device, like computer), and then does something illegal, it’s going to be hard to show that the person who did it wasn’t you, unless you can show timing-wise that it wouldn’t have been possible (e.g., you were in the hospital in a coma). There likely are no technological fingerprint traces going back to your friend’s wife. Though a lawyer could perhaps raise reasonable doubt if they are able to demonstrate that more than one person had access to the device.
Now if the phone were truly hacked (i.e., she installed spyware), it might be possible to uncover that spyware and get a court order to get information from the spyware company about what account/email address is being used to control the spyware and from what IP address. That might show a connection to his wife if she’s not smart enough to cover her tracks through a disposable email address and anonymous proxy. Again, this is something that he would have to discuss with his lawyer.
My theory is that we are all being naive to think that someone can not hack your phone without being physically on it. If elon musk can send a roadster into space for the heck of it and the whether can be controlled by space hubble/ satellite you seriously don’t think these people can remotely mess with your phone! Maybe drones are capable if it needs to be close. And personally I believe that Google and facebook are definitely coordinating and orchestrating the tapping of conversation and you take the big 6 of technology and the big six of the movie industry and you realize that they are not only stealing your content and conversations and ideas to get more rich than they already are but it is because there is a much larger purpose and that is the next generation and World domination. Just my opinion think about all the big FB Google Microsoft companies joined forces and can control every darned thing from your tv to your washing machine to your headphones your credit card there is nothing stopping them from controlling even our president and the government
Many of the security products that performed very well in AV Comparatives’ testing did quite poorly in my spyware test, notably Kaspersky and Eset.
Great blog. This blog is very useful. Thank you so much for giving plenty of awesome information. I appreciate all your work and also providing a lot vital ideas for your readers. Thanks a lot…
NON JAIL BROKE Apple I-Phones ARE VULNERABLE. Top-Spy products and others guarantee it. Maybe their products for I-phone were released after this article but I assure you the products are out there and easily found. And of course we recently heard the report about our very own government spying on I-Phone users. NOTHING is safe from spyware if its electrical, Apple admits this week they were SHOCKED at what has been going on and called it the “Worse nightmare you will ever have when you find out how serious the espionage of our own government against its citizens is.”
I have yet to see any spy app that can work on a non-jailbroken iPhone. Top-Spy states explicitly on their site that the iPhone must be jailbroken to install and requires physical access to the phone. All spy apps for iOS that I’m aware of also stopped working on iOS 6.1.3 and later.
Even the NSA spying seems to have been based on “close access” methods and targeted early versions of iOS (which we already know was vulnerable to various types of malware after jailbreaking): http://allthingsd.com/20131231/apple-says-it-is-unaware-of-nsas-iphone-backdoor/. I certainly wouldn’t declare it impossible that the NSA has advanced its methods, but the most powerful spying organization on earth has tools and access beyond the ability of your typical jealous spouse.
If there is a spyware app out there can can prove to me it can be remotely installed without jailbreaking the iPhone, I would love to hear from them.
hi Josh , iphone applications can have there coding remotely configured to allow access to an insecure port 62078. To achieve this the hacker uses the existing app’s sql to flash the phone which leaves the hardware vulnerable for 10-30s allowing the information to be read and the app’s code is adjusted. The iphone reboot with an app that now can be used to collect and send data over cellular or wifi connection.
The best iphone application to keep a close eye on the phone is ‘System Status’. View the connections to the iphone. Secure iphone apps use port 80 & 443.
Turn Safari off in restrictions and download Mercury for private and secure internet.
I wasn’t aware of this particular risk. Can you provide a link with more details on exactly how this works and whether it is still applicable to current versions of iOS? What I was able to dig up seems to suggest this may have been corrected in iOS 7?
Also, in researching your issue, I did find other means that iPhones could be hacked by using the trusted connection iPhones make with computers and wireless networks, so that someone with access to that network could security holes that were part of iOS. Fortunately, those holes have been plugged in iOS 8. FOr more info: http://www.zdziarski.com/blog/?p=3820
I have an android phone and i was talking to someone in LA and he was traveling to India with contract to build hospital in New Deli. We have never met but still talk India to me in SD. I noticed his India #an LA# plus four other India numbers. It was in whatscall. I watched a number call a number i had called an watched those numbers call my contacts. No access to my phone but India numbers in whatscall with access to all my calls an contacts. How is this possible? Are they reading my sim card or what. I told him what the heck is going on with 4 India an his LA numbers in my phone. He acted like dumb an next day all India nums were changed. Im freaked out and need your expert advice. Thank you kindly. ASAP
I am pretty sure my phone sim card has been compromised with spyware software. I thought it and now I am very sure. The problem is though it is just not my phone it appears to be rooted in my sim card. I have changed phones and have the same problem. But on one particular phone, a Patech, which if not a Iphone, but a flip phone. I receive odd text messages with numbers and symbols. It is like that one phone gets the text while the others don’t. The texts are sent from a unidentified number. How can I find out what number the text is is coming from. It is important to me that I find out who bought the software and when it was put on. Like I said it seems to be the sim card infected. But before I rid myself of my phone I what to know what kind software it is where and when it was installed on my number. Can I trace that weird text I get so many of? It begins with vvm.mobile.att.net,5400?f=0&v=, then has my number and a bunch of symbols and numbers. I google the whole number and came up with nothing other than I do know now vvm.mobile.att.net takes me to their Visual Voicemail. A service I do not have and did not know existed. I am going thru a divorce and my husband has been very vicious through out. How can I find out where these text are coming from and how to scan my phone to see software.
First of all, why do you think your cell phone or SIM card is hacked? Is it just the odd text messages? That doesn’t sound like a sign of hacking.
Visual voiucemail is a real service on Android. You may not have it active but those could be promotional texts from AT&T that are coming up garbage on your non-smart phone. Not sure why that would be, but could be the case.
You can always go to your AT&T store to get a new SIM card if you think your current one has been compromised, and follow our recommendations above for checking your phone for spyware. But, so far, I’m not hearing anything that sounds like a hacking problem.
In terms of tracking spyware that is found, that’s nearly impossible to do. The best you could probably hope for is to work with your attorney to trap the spy by placing false information and seeing how the spy (presumably your ex-husband) reacts.
Those texts are AT&T’s voicemail system notifying the phone that you received a voicemail. You don’t have to have visual voicemail in order to receive them. On most phones, those texts never show up in your text messaging history, but some phones don’t know how to handle them and display them to the user instead of hiding them. They’re nothing to worry about.
Hi,
in Google Play there are several anti spyware apps. As few examples I may say “Anti Spy Mobile”, “Malwarebyte” or “Privacy Scanner”.
Did you try any of those?
If yes, what were the results?
Regards
JB
Generally, I would never recommend downloading a “no-name” antimalware app from Google Play. The likelihood it would actually work is slim. Or so I thought…I gave the three apps you mentioned a go and here are the results:
- Malwarebytes is certainly a well-regarded player in the PC security space - it is my “go-to” app as a backup to my main Norton Interet Security program. But on mobile, Malwarebytes is a bust. It only found two of the spyware apps above and neither of the two new ones I’m testing.
- Privacy Scanner was better, but not by much. It found four of the spyware apps above, but neither of the two new ones.
- Anti Spy Mobile was the real surprise. It found all nine of the apps above (better than any of the “big name” programs did their first time through) and discovered one of the new potential spy apps I’m testing, Cerberus, which pretty much every big name vendor missed. (note: it’s possible that Anti Spy Mobile updated their database with the samples in our study, though, based on noted on their site, they have clearly been tracking many of the amples for some time). Better yet, it scans very quickly.
Thanks for making me this other option!
I don’t know where to begin!
1. You have 9 apps and are talking about percentages!
2. Out of the 9 apps, only 2 are in the Google Play Store (which is exactly what the Anti-Malware authors are stating - that Malware gets removed quickly if it gets on the Play Store).
3. Both the apps in the PlayStore - MobiUcare and SMS Tracker are CLEARLY meant to be used to track your phone if you lose it!
4. If you are installing the app, clearly, you wanted to. It’s not Spyware if you intentionally installed the app. It’s spyware if it’s collecting personal information and sending it to a server without your knowledge.
5. Your advise is to reset the phone if you have ADB enabled!
...
There is so much you could have done with the topic. I agree with you that these apps should show up as potential malware. But as always the hysteria about Android malware out in the wild (and nobody denies that) doesn’t jell with an infection rate of 0.001% when installing apps from the Play Store. If you want to pirate apps or side load apps from non reputable sources, then really you have only yourself to blame.
There are a lot of apps that scan through app permissions. https://play.google.com/store/search?q=permission&c=apps. I’m sure that at least one of them will be less geeky and will show a non techy user categories of spyware.
Did you actually read my story? This is about anti-malware software’s ability to detect spyware that someone has installed on your phone to spy on you (e.g., a jealous boyfriend or spouse), not something you download by mistake from Google Play or a third-party market. Most of the antimalware apps I tested do a very poor job at that, and it doesn’t matter whether the spy apps come from Google Play or not.
Where the anti-malware vendors and I strongly disagree is in the definition of what should be considered “malware.” Their position, similar to yours, is that an app like MobiUCare should not be detected because it is “intended” to be an anti-theft product. My position is that it shouldn’t matter what an app in “intended” to be. If it can easily be used for malicious spying, then anti-malware apps should flag it and the user can decide if it is there validly or not. FWIW, the anti-malware apps also missed a fair amount of the outright spyware apps, too, so the testing was really a complete bust no matter what your philosophy is.
I’ve looked at the app permission angle quite a bit and concluded it’s also a bust. The spyware app permissions are no different than the permissions of numerous other apps on your device. For a non-sophisticated user to figure out from the permissions which are valid and which are spyware would be extremely difficult.
As an example, I recently had an issue with malware on my device and spent considerable time going through each app permission in great detail to identify the culprit, to no avail. Finally figured it out when one of my anti-malware apps detected it (and the other six I tried missed it). Was an app that was on Google Play and then went rogue with incredibly intrusive adware (as in constant pop-ups, browser redirects, etc). Not spyware, but an example of the difficulty of using app permissions. The app actually had been removed from Google Play at some point, but users are never notified when a downloaded app that once was valid goes bad…
..and I think that you are in fact incorrect in what these apps are meant to do. If I have installed these apps to protect/recover my phone from theft, the last thing I want is for the thief to run a scanner app, find my app and remove it.
You are making two points. First, someone other than you installed the app and you want to find it. For that, you will have to have lost control of your phone. If your wife/girlfriend/colleague has messed with your phone, you need to be in a different relationship and be careful with your device. But this requirement directly violates your ability to protect/recover your phone. And I stand by the vendors in this respect. I would never spy on my wife or kids. But I have no doubt that there are plenty of folks who do and in fact consider it their parental duty. In this case, I’m okay with Anti-Spyware apps not reporting these. But it’s really not difficult for someone to create apps that will actually report all spyware. But it helps slightly if it’s not one of the well known anti-malware apps.
The second scenario you came up with are apps that are show annoying popups and re-directions. A few years ago, apps started showing ads in the notification drop down. It got annoying as hell. I installed Addons Detector (https://play.google.com/store/apps/details?id=com.denper.addonsdetector) making it drop dead easy to weed out these apps from my device.
I do accept that it’s not easy for mainstream users to understand what all the permissions mean. Sometimes, it’s difficult even for developers. And I agree that Google should work on this and make it easy to understand. I haven’t looked to see if there are apps that make it easy to understand permissions. I use Permission Explorer (https://play.google.com/store/apps/details?id=com.carlocriniti.android.permission_explorer) and they do provide categories of permissions. So you don’t have to go through each app. If you can identify the category of the permission then you should be able to narrow it down.
In your spam scenario, I don’t know if Addons Detector would have worked. But your argument of a number of apps using the same permission legitimately doesn’t hold water since that’s exactly what you are asking these anti-spyware apps to do. There are either going to be a lot of false positives or they are going to miss the apps all together.
Obviously not feasible for the mainstream, but when I find a difficult to detect spam app, what I do is wait for the popup to appear. If it’s not modal, I run catlog. Clear the log, set it for recording, go back to the popup and click on the button. Go back to catlog, stop the recording and look at the log. It will show you the offending app or at least greatly narrow it down so you can then look at its permissions.
Again, not something my wife will do. But there may be an app that automates this.
All my Android devices are immediately rooted. If you are rooted, XPrivacy is a great app to install
https://play.google.com/store/apps/details?id=biz.bokhorst.xprivacy.installer
It gives you granular (line-item) permission access to apps. Unlike AppOps which prevents an app from accessing a permission, this provides fake information. Denying an app permissions can cause it to fail. This doesn’t.
It is only tangentially relevant to spyware detection, but I thought it could be of use to others if they were not aware of it.
Any thief with half a brain can get around the theft tracking apps by simply searching for and deleting them or factory resetting the phone. They don’t need an anti-malware app to do that. And if I were a half-brained thief, the first thing I would do is put the phone in airplane mode, which would kill the tracking ability of any anti-theft app. Really dumb thieves may not know this, but they’re probably too dumb to run anti-malware, anyhow. For the professional phone thieves, your phone is as good as gone the moment they take it.
The issue of spousal spying is not hypothetical. You can read the numerous comments in our original spyware story (https://www.techlicious.com/tip/is-someone-spying-on-your-phone/) from people whose lives are being turned upside down by an abusive relationship. And those comments are the tip of the iceberg. I’ve received numerous personal emails from people in the same situation and even been contacted by a computer forensics expert who is working on uncovering mobile spying in a divorce case.
It’s all well and good for you to say these people should be in a different relationship (most of them would agree with you), but that horse has left the barn. It’s not the position of anti-malware vendors to only protect people who do everything right. If that were the case, we wouldn’t need anti-malware at all - no one would be in bad relationships, no one would click on phishing links or visit sites with drive-by malware. The fact is, these companies specifically market their products as protecting against spyware and, for the most part, they do a dismal job at it.
p.s. To be clear on how anti-malware works on mobile (as opposed to computer), almost all of it is based on looking for specific app signatures or names (e.g., with the apk), not heuristics. So stopping spyware (or any mobile malware) is a matter of manually identifying the bad apps and flagging them. So you won’t get false positives, any app flagged will be one the security vendor has specifically identified as malware.
Thats so true with the car keys becuase nobody will want car keys anymore to start the car and then they have to unlock the door and then thats how its going to go
Hi, Thank you for your article. I believe I had spyware on my old phone and have good reason to believe it was a co-worker. I got a new phone and wonder if the spy app can be transferred to my new number since my number didn’t change. One call to a co-worker kept cutting off during a conversation. I kept calling her back and it kept cutting off. That made me feel suspicious. I have been very careful not to let my new phone out of my sight. I have kept it closely on my at all times while at work. I am feeling somewhat insecure. Do you think this is possible? I appreciate getting a reply from you. And thanks again for your article.
I haven’t seen any commercially available spyware that would allow you to install without physical access to the phone. If you have a secure lock code on your phone, that would prevent someone from installing spyware, even if they had access.
But I wouldn’t get concerned over one bad call. If this is a ongoing concern for you I recommend you install TrustGo on your phone to scan for malware.
Ive had battery issues, odd vid i didnt take, camera issues HAD IT ALL for over a year. I, too began to think my roommate was remotely reinstalling spy apps. PLEASE reconsider the people whom you TRUST!! Come to find out.. it was a friend I completely trusted. A friend i confided all of this too. As i pushed my roommate boyfruwnd further away thinking he was the best liar EVER.. ugh. I researched and researched. All the while telling what i knew to a best friend. So understand_ remote i stall is still not possible and its time to lookat WHO can see your passcode. I must say that pass codes are visible to hidden cameras placed above and behind your favorite chair or toilet. Keep your eyes open guys!
It is, unfortunately, experiences like this that demonstrate why spyware is so disturbing - it’s those who are closest to you who are the ones violating your trust and privacy.
A year on, this has to be one of your best posts of 2013. Any chance of a repeat to see if anything’s changed in 2014? Has anything come of it?
This is a tricky area to test because identifying new spyware programs and getting access to them is not an easy process. Most of the vendors in this test updated their files after this article to cover the gaps I identified. Amazingly, a couple neither responded to my messages nor had updated their software when I checked a number of months after the testing. How you can call yourself a mobile security company when you don’t fix these obvious holes is beyond me.
Anecdotally, I’ve found recent examples of well-known potential spyware apps (such as Cerberus) not being picked up by the vendors (TrustGo being the exception), so I still don’t think most are taking this seriously. One vendor, Sophos, told me they consider apps like Cerberus safe because they have valid anti-theft uses, even though those same features can be turned against phone owners by malicious parties. It’s the same PUA debate I discuss above. You be the judge on whether you agree with their position.
In the meantime, TrustGo is my recommendation for antispyware both for it’s initial performance and for being the one vendor in my recent test to flag Cerberus.
I take the same POV as you have done: detect, notify, give choice.
One other package to look at is LBE Security Master, a Chinese suite that’s apparently well enough regarded for XDA developers and Xposed repo to have a thread and module devoted to making it available in English. I don’t know how that one stacks up, as it doesn’t have English reviews, but curious how it handles this issue.
“Most of the vendors in this test updated their files after this article” .. this is why I wondered about an update.
(I don’t think the PUA thing stacks up; after all, the same antimalware companies don’t hesitate to provide banner and spam detection/blocking, but hey, those could be “potentially useful” too, especially banner ads…)
Can someone pair their phone to yours via Bluetooth if they had access to your phone? I noticed a long number paired to my iphone5s today. Also SGH-T on iPad was listed under devices discovered but don’t think it paired since it did not give me the option to forget device like the iPhone did. Any new updates on iPhone users being tracked or spied on without a jail break?
Yes, they could pair their phone to yours if they had access to your iPhone. But I haven’t researched what level of access Bluetooth pairing would allow on your iPhone. You an always forget any devices you’re not familiar with and repair them later if you need to.
I have yet to see any spy apps for iOS that can be used without jailbreaking, and I’m skeptical that there are any out there. However, anyone with access to your iCloud account could easily spy on you that way if you use iCloud to backup your iPhone or iPad.
I just want everyone to know ,i dont think there is a way to secure a phone or a computer ,ive actually become obsessed with learning about how to block or secure each new way ive been comprimised,just when i think ive got everything set, i get surprised as hell,by the new and more technical ways these hackers use.and in recent security breaches , i have no doubt that these people are some type of developer,the main reason most of these companys
dont have a complete security package.is because there is all kinds of hidden back doors in windows that most people wouldnt even know about.especially win.8.1. and now with the sync of all accounts and devices ,the worst being bluetooth,any app can easily obtain your personal info.I turned on sync my gmail account with all devices ,only to find that people in my circle ,appeared on my android phone numbers list..if i have theyre info, im sure they have mine.now i will not sync anything ,anyone with a vodaphone can place a bluetooth directory remote connection in the system settings and listen in with out you even knowing ,they use the new window 8.1 enumerators as virtual connections .and win 8.1 has a large amount of them.i cant believe how i fished out and found the sources of most of the breaches.the latest one im dealing with is the use of windows caculator, this app has all the tools to remotely program your binary files in the registry database using any standard 2.4 gig hz RF frequency such as a remote keyboard ,mouse ,stereo ,t.v,wireless usb wifi, a cordless phone ,even a garage door opener.its called a universal remote.you can down load this free from google apps.this is a True fact ,i have GFI endpoint installed ,and i have locked out my devices , to my astonishment ,they are trying to now access my dvd writer constantly.as well as the wifi adapter ,This GFI endpoint is awesome it also protects the sql servers ,I also tried one of theyre tricks and programed the bluetooth as a different useless device. BIZARRE things to really watch for.
1. Notepad is used to change system ini settings from desktop to C:\users\your name\ appdata\packages where they can control everything
2.taskmanager is going crazy with 100% disk and cpu use.. they get you to delete junk EXE files in the recycle bin .the recycle bin has 3 hidden folders one is a account unknown. they can build a database in the free space where deleted files are kept and rewrite them. finally some how they have cleanup delete a secretive file no one wants to talk about , called NET EFFECTS SIXTY FOUR DOT E X E , a windows metro control file
3.if you have a ethernet connection they can access and program your computer after you shut it down.the folder recycle bin now shows in the bios under boot options.
4. this is all from a simple down load of a app.
and this one is called ASIMPLEBROWSER by a sheik majeed. from windows store. DO NOT DOWNLOAD ANY APPS.
so if you download a pic from your android to the computer ,im sure the sd card can be compromised.
What a blog! Wow!!!
I had no idea this even stuff even existed and I found this site by “accident”. There are no coincidences.
Josh, I really wish I could ask you a few questions privately.
Honest to Pete.
My iphone is, indeed, compromised due to potential Work Place Violence .....
Please .... Do not post this .... contact me if you want to.
Obviously, I work night shift.
This is from my ipad, not iphone.
I want to personally thank Josh, because he did, indeed, respond to me privately and we had several email conversations pertaining to my iphone5 and its “possibly being compromised” due to a work place situation. I have since factory reset my phone and was able to update my iphone. Apple definitely dropped the ball on this one.
I am hear to tell ALL of you ... PLEASE follow what Josh suggests ... especially the password lock screen, blue-tooth and SMS texting ... and PLEASE NEVER LEAVE YOUR PHONE unattended. He absolutely knows what he is talking about!
I could be wrong, and correct me if I am, but, I also suggest disabling icloud, locations and even putting it on airplane mode—- should you suspect something is just “not right in River City” when you are at work. I had ALL the “symptoms” of “spyware” or whatever you want to call it, being on my phone, but was not educated in this area. By the Grace of God, my mind never in a million years thought of this or to even do it to another person, but, IF a “company” has something to hide ... well there you have it. Shortly after my last e-mail to Josh, our local news did a segment on “cell phone tracking” ... Interesting .... the equipment to do this costs $300k and many “investigators” already have this equipment. The phone you have does not matter…. if your phone is not locked, you have your icloud enabled, anyone can download “spyware or whatever” on your phone in less than a minute or access your information and you would never know it and it is hidden so well its ALMOST impossible to find and they can track EVERYTHING YOU DO .. from pictures to texts to e-mails to phone calls. The company I worked for has some “serious” investigators” to protect their interests for other reasons, it wasn’t just about me.
I did not have a lock screen enabled on my phone—it just never occurred to me to do it. BIG MISTAKE. At work, I left it unattended as I played music from it, I KNEW a certain person had distracted me while another “did whatever they did” to my iphone. The MAJOR clue something wasn’t right—I was UNALBE to update to 8.0 .... I would receive double or triple e-mails/texts, INCREDIBLY high usage, battery would drain like crazy, delays in sending texts/email or not getting a text back for HOURS or until the next day. MISSING text messages/emails that I KNOW I sent—there one minute—gone within hours. On and on it goes. This started almost immediately after the “event” of being distracted. Looking back, I think, how could I have been so naïve?
Your iphone does not have to be “jail broken” to have this happen. I learned this the hard way. After WEEKS of this, what I did was send a VERY DETAILED text to a person ... on purpose… just to see what would happen and it cost me my job. I was “laid off” within 12 hours. Hmmmmm
Its not over yet, I have a long road ahead. The best part ... I did not have anything to hide .. they did. There are no guarantees in life and whether you believe it or not, I know God has me covered on this. I am open to knowledge based comments.
Thank you again, Josh, for your input.
I read through most of these postings and didn’t see what I was looking for.
If an ex is tracking my phone, is the spyware tracking my SIM card? I guess what I’m asking is, if I put a new SIM card in my phone, is the new one able to be tracked?
Diane
If someone is tracking you via spyware installed on your phone, then putting in a new SIM card wouldn’t make a difference, because the tracking is happening through software installed on the device. If someone is tracking you via a “family tracking” feature on your carrier account, then putting in a new SIM card also wouldn’t make a difference.
Thanks, I appreciate the feedback. I guess I assumed that all the phone information would be on a SIM card and a new one would prevent it from being tracked (as far as texts and calls and such).
Thanks again!
HELP there everwhere I mean the tracking and loging into my account what should I do I just bought a I pod touch and ipad for my wife but it seems that their connectected to them both plus my phone wich I use as a hotspot for the devices I don’t wanna get feds involved but how much is going on I need help and BADLY!!! I just recently found android mng, on the devices how can I get them off and leave me alone
Can you explain more clearly what issue you’re having that you think is related to phone spying?
I have been using the app lookout on my phones for quite some time. I only today put it on my newest phone because i noticed a decrease in speed and functionality of the device. Once it scanned my phone it found surveillanceware hidden under a running file called “system core”. Could you possibly tell me what app it could have come from or how it got on my phone?
If Lookout provided more info in its report/log, that would help. Otherwise, I don’t have enough info to clarify the issue.
You cannot install security software to detect or remove any type of infection. I’m sure Norton’s was the best and it tells you this on their website, why they offer a free boot & scan utility before installation. Second of all, more like “it” PERIOD, is, you cannot protect anyone that will click and open “anything” with “ANY” protection software. You do not recognize something, delete it.
Nuff said.
bye
Thanks, this is very helpful.
but please…
Don’t respond to trolls who are obviously making money selling spyware.
It is a MASSIVE industry. There is big money changing hands, and official agencies are also doing it any time they feel like it.
Just delete their troll posts, nobody will think less of your work.
Excellent article, please do more research and post it.
:D
How and why is my phone and my husbands iphone 5c getting the same text but only from one person it is his ex wife . The other night i was shopping when i look at my phone and i saw text coming and going it was her number i saw her talking to mu husband and her responding we r both pretty freaked out over this she has done this to him when they were getting divorced she has no access to our phones can u plz help me here
patty
Read More Comments: 1 2

From Gary on July 19, 2013 :: 2:36 pm
Excellent article !!
Sure glad that I don’t use cell phones !
Reply